Andrew W. Appel's
Studies of Voting Technology

Andrew W. Appel'sStudies of Voting Technology |
 |
Recent articles on voting:
Examination Report on the Hart Verity Vanguard 1.0 Voting System, by Andrew W. Appel, October 2025. [local copy]
An Internet Voting System Fatally Flawed in Creative New Ways, by Andrew W. Appel and Philip B. Stark, arXiv:2411.11796, November 2024.
24 for '24: Urgent Recommendations in Law, Media, Politics, and Tech for Fair and Legitimate 2024 U.S. Elections, by the Ad Hoc Committee for 2024 Election Fairness and Legitimacy (Appel, Azari, Cain, et al.), edited by Richard L. Hasen, UCLA Law School, September 2023.
Is Internet Voting Trustworthy? The Science and the Policy Battles, by Andrew W. Appel, University of New Hampshire Law Review, 21 U.N.H. L. Rev. 523 (2023).
Evidence-Based Elections: Create a Meaningful Paper Trail, then Audit, by Andrew W. Appel and Philip B. Stark, Georgetown Law Technology Review, volume 4, pages 523-541, 2020.
Ballot-Marking Devices Cannot Assure the Will of the Voters, by Andrew W. Appel, Richard A. DeMillo, and Philip B. Stark. Election Law Journal, 2020. (Non-paywall version, differs in formatting and pagination; earlier versions appeared on SSRN.)
Fair Elections During a Crisis: Urgent Recommendations in Law, Media, Politics, and Tech to Advance the Legitimacy of, and the Public Confidence in, the November 2020 U.S. Elections,by the Ad Hoc Committee for 2020 Election Fairness and Legitimacy (Appel, Azari, Cain, et al.), edited by Richard L. Hasen, UCI Law School, April 2020.
Securing the Vote: Protecting American Democracy, by National Academies of Science, Engineering, and Medicine: Lee C. Bollinger, Michael A. McRobbie, Andrew W. Appel, Josh Benaloh, Karen Cook, Dana DeBeauvoir, Moon Duchin, Juan E. Gilbert, Susan L. Graham, Neal Kelley, Kevin J. Kennedy, Nathaniel Persily, Ronald L. Rivest, Charles Stewart III. September 2018.
Five-part series on the Swiss e-voting system:
|
Video demonstration of how to hack a voting machine The New Jersey Voting-machine Lawsuit and the AVC Advantage DRE Voting Machine |
New Jersey Election Cover-up: During the June 2011 New Jersey primary election, something went wrong in Cumberland County, which uses Sequoia AVC Advantage direct-recording electronic voting computers. I served as an expert witness in the resulting lawsuit. From this I learned several things; see the attached report.
Security Seals On Voting Machines: A Case Study, by Andrew W. Appel. Accepted for publication, ACM Transactions on Information and System Security (TISSEC), 2011.
Abstract: Tamper-evident seals are used by many states' election officials on voting machines and ballot boxes, either to protect the computer and software from fraudulent modification or to protect paper ballots from fraudulent substitution or stuffing. Physical tamper-indicating seals can usually be easily defeated, given they way they are typically made and used; and the effectiveness of seals depends on the protocol for their application and inspection. The legitimacy of our elections may therefore depend on whether a particular state's use of seals is effective to prevent, deter, or detect election fraud. This paper is a case study of the use of seals on voting machines by the State of New Jersey. I conclude that New Jersey's protocols for the use of tamper-evident seals have been not at all effective. I conclude with a discussion of the more general problem of seals in democratic elections.
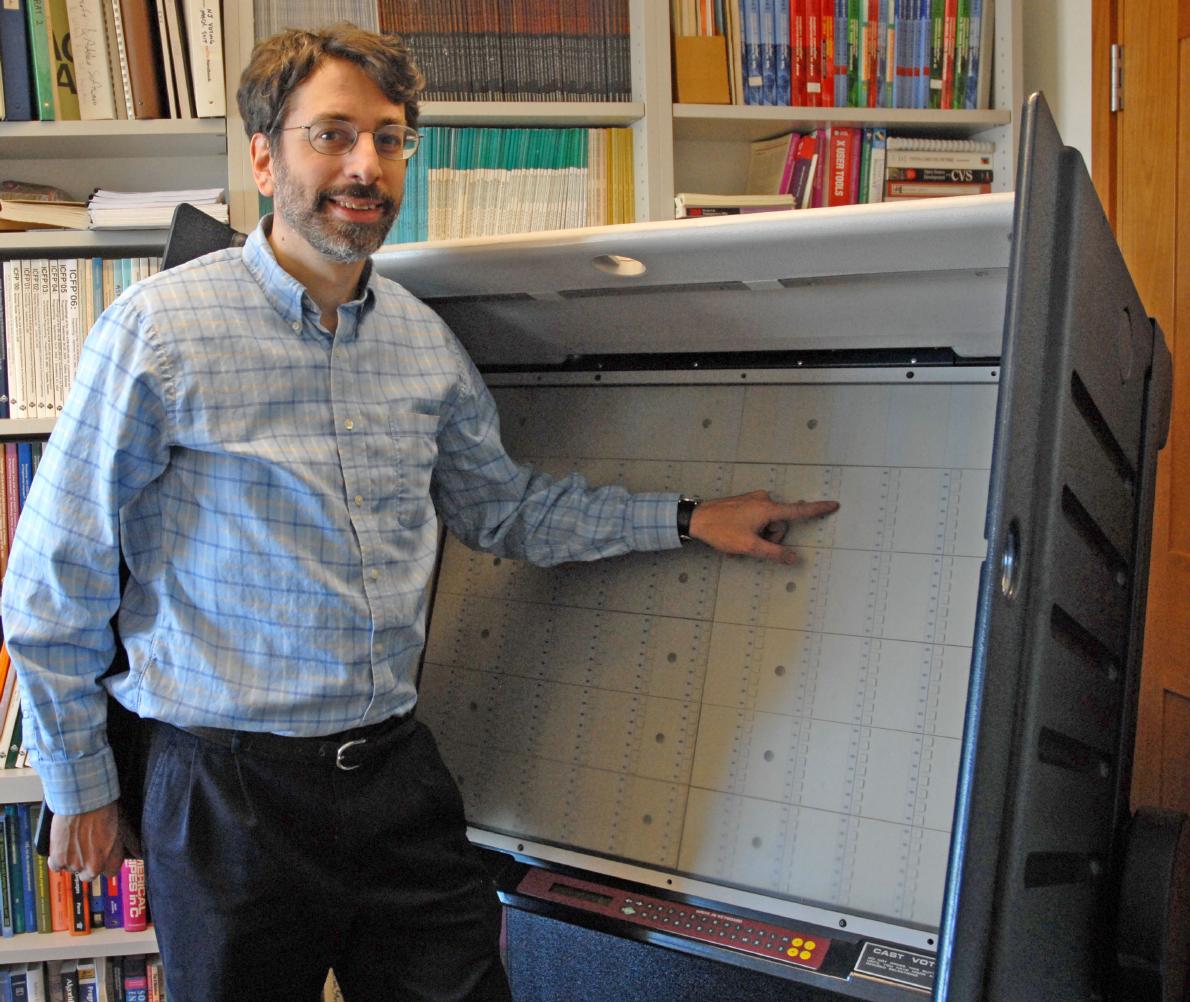
Analysis of the AVC Advantage DRE voting machine: In July 2008 I led a team of computer scientists in a study of the software and hardware of the Sequoia AVC Advantage. This is in connection with the NJ voting-machines lawsuit.
Summary article:
The New Jersey Voting-machine Lawsuit
and the AVC Advantage DRE Voting Machine,
by Andrew W. Appel, Maia Ginsburg, Harri Hursti,
Brian W. Kernighan, Christopher D. Richards,
Gang Tan, and Penny Venetis.
Published in
EVT/WOTE'09, Electronic Voting Technology Workshop / Workshop on Trustworthy Elections, August 2009.
Technical reports:
 |  |
| 6300 beads representing the precincts in a New Jersey Governor election; 10% of the beads are blue, representing fraudulent voting machines. A 1% sample (63 beads) is shown; it is extremely likely to include at least one blue bead (in this case the sample has 7 blue beads), and thus the audit will catch some of the fraudulent machines (triggering, in principle, a wider recount and a forensic investigation). | 100 marbles representing the precincts of a city mayoral election; 10% of the marbles are blue representing fraudulent voting machines. A 1% sample is shown (one marble); it's unlikely that a 1% sample will include any blue marbles. While a 1% audit works well for statewide races, it does not suffice for local or legislative-district elections. (Photos: Alex Halderman) |
Related papers:
The Trouble With Triples:
A Critical Review of the Triple Ballot (3ballot) scheme, Part 1
by Charlie Strauss, October 5, 2006.
A Critical Review of the Triple
Ballot Voting System. Part 2:
Cracking the Triple Ballot Encryption
by Charlie Strauss, October 8, 2006.
